Finding a Secure Baby Monitor Is Much Harder Than You’d Think

If you are in a situation where you need to buy a baby monitor (camera), you probably want to choose something secure, right? For most of these devices, security is an afterthought, and anyone with some technical skill and time on hand can listen to whatever happens in the baby’s room. It is even worse when someone outside the family can talk back through the baby monitor. And, worst of all, when someone can watch the live feed of the mother breastfeeding the baby.
So, knowing that it is in every parent’s best interest to buy a secure baby monitor or camera, let’s see what the vendors offer.



They claim that their baby monitor is secure if it:
- Does not use Wi-Fi but uses FHSS.
- Does not use Wi-Fi but uses DECT.
- Uses Wi-Fi but not cloud.
- Uses Wi-Fi and a secure cloud.
That seems confusing, doesn’t it? The bad news is that none of these options are secure by default. Let’s discuss the different technologies in a bit more detail.
Plain Radio Signal
Nowadays, it’s hard to find a baby monitor that uses a fixed frequency and unencrypted communication, but this was not the case in the past. If you look up RTL-SDR tutorials, you’ll find many tools and software that let you snoop on these insecure devices (as well as some satellites and weather balloons).
FHSS
“Frequency-hopping spread spectrum (FHSS) is a method of transmitting radio signals by rapidly changing the carrier frequency among many frequencies occupying a large spectral band.”
https://en.wikipedia.org/wiki/Frequency-hopping_spread_spectrum
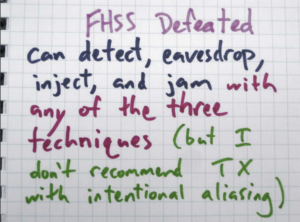
FHSS was developed more than a hundred years ago, in around 1903. Vendors usually claim it is secure, but it is not. FHSS only “obfuscates” the physical radio signal. The only real advantage of FHSS is that anyone who wants to snoop on the connection has to be physically nearby. While this is a good security feature, it may not be enough.
DECT
This standard was developed in 1988. It is better than FHSS, but it still does not provide great security.
“Digital Enhanced Cordless Telecommunications, usually known by the acronym DECT, is a standard used for creating cordless telephone systems for IoT systems. […] The standard also provides encryption services with the DECT Standard Cipher (DSC). The encryption is fairly weak, using a 35-bit initialization vector and encrypting the voice stream with 64-bit encryption.”
https://en.wikipedia.org/wiki/Digital_enhanced_cordless_telecommunications
DSC has been broken, and anyone can download free software tools to decrypt the original DECT encryption in real-time. There are also better, improved DECT standards, but I have not seen any proof that any baby monitors or cameras use improved standards like DECT-NR+. I assume that if a vendor claims their product is safe because it uses DECT, it almost definitely is not secure.
Wi-Fi, No Cloud
Buying a baby monitor that uses Wi-Fi without a cloud is exceptionally hard. This category is mostly for DIY baby cameras. This might sound fun if you have the technical skills to build your own devices, but I am not sure you will have the free time to do this once there’s a new baby in the family.
This solution can be fairly secure if no cloud access or port forward is configured in the home router. For remote access, I recommend configuring a Wireguard or OpenVPN server for your home network and just using the VPN every time you want to access your network. This way you’ll have secure remote access to your home devices without exposing any of your ports to the Internet.
Many cameras use both direct remote access (with ports open to the Internet) and remote access via the cloud. If a camera opens ports for remote access on the home router via UPnP, chances are that hackers can access your camera. There are countless vulnerabilities in these types of IoT devices; their vendors have bad reputations, and, based on our report, this is the most vulnerable type of device among all IoT device types.
Wi-Fi with Cloud
This group of baby monitors is the most complex and could merit a separate article. Why? There are too many components to consider. To keep it short, here are the key points and recommendations to consider before buying a baby monitor with a cloud connection:
- Only buy devices from a trusted vendor with a good track record of patching security vulnerabilities. Devices in the Apple HomeKit and Google Home ecosystems are usually a good start. If you choose these devices, make sure to keep them up to date and patched.
- Make sure that data in transit is adequately encrypted (e.g. AES-128 is pretty good).
- Find out whether data in the cloud is encrypted so no administrator (or hacker) at the cloud operator can look at your camera feed. HomeKit is known to encrypt camera recordings. Unfortunately, if the video feed is not encrypted while stored in the cloud, the video feed can end up in places you don’t want.
- Check whether multi-factor authentication is configured to access the feed.
- Use a unique, randomly generated password to access this service.
- Use a unique, strong Wi-Fi password and a separate guest network for people visiting your home.
Unfortunately, there are not that many devices that check all of these boxes.
Conclusion
There are many other factors that go into choosing a device, such as price, functionality, ease of use, etc. If you want an audio-only device (no camera feed), FHSS or DECT is probably a good choice. Whichever device you choose, anyone nearby could still probably use a parabolic gun spy microphone to listen to the audio, or your device speakers might unintentionally act as microphones and RF transmitters.
But if you are using a baby monitor with a camera and the mother is about to breastfeed in front of it, maybe turn it off or change its angle for that time. The same goes for the Wi-Fi solutions.
So, is there a conclusion? I don’t really have one, I just hope you learned something today. Especially that if vendors tell you something is secure, it might not be the case.