How I Got $88 from a WhatsApp Scammer And “Forgot” to “Reinvest” It
Warning: Don’t try this at home! Following these steps might involve you losing money. You have been warned!
UPDATE: After sharing this story I got contacted by “recovery services” scammers and wrote a short part 2 of the story: Dont’ Get Scammed Again: No One Can Recover Your Lost Funds.
It all started on the 17th of December. The weather in Budapest was bad, and it was a lonely Saturday at home when I got a new message on WhatsApp.
I was thrilled.

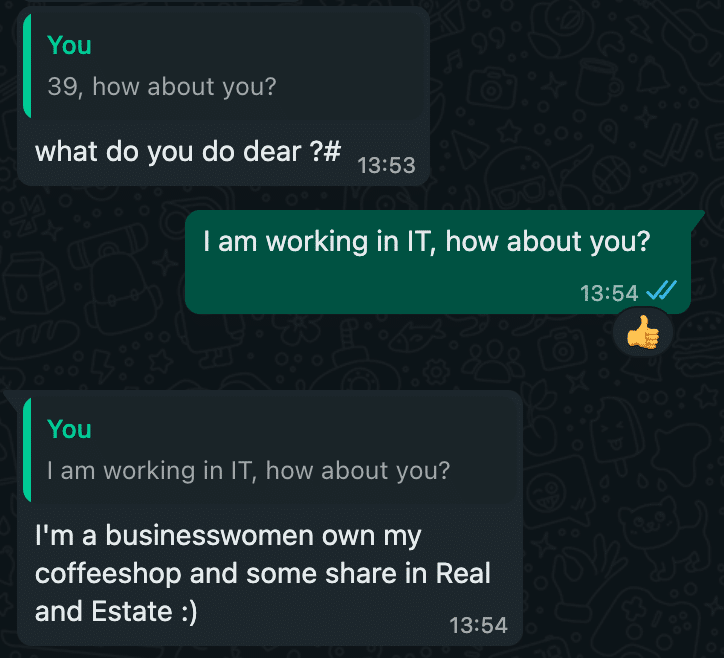
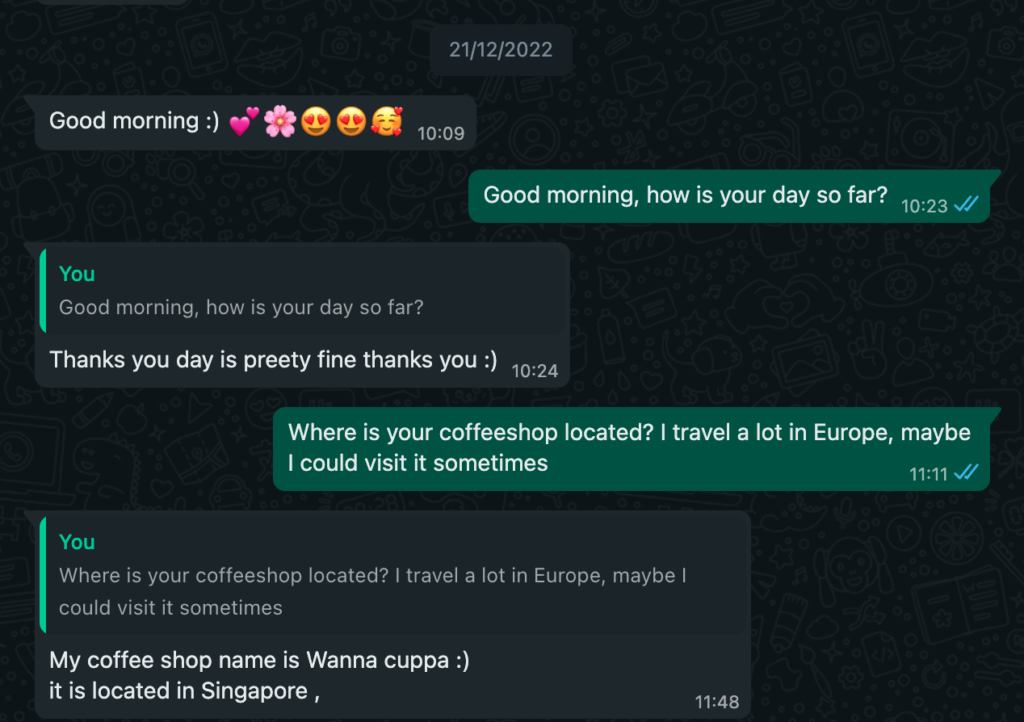
As luck would have it, a nice young Asian woman contacted me accidentally, and we started chatting. She said she lived in Singapore and was interested in visiting Budapest. She was also a businesswoman, running her own coffee shop and had shares in “Real and Estate”.
Then, like a mugger trying to take me to a secondary location, she asked me to contact her on her personal number because this was her “traveling” number.
And I immediately did.
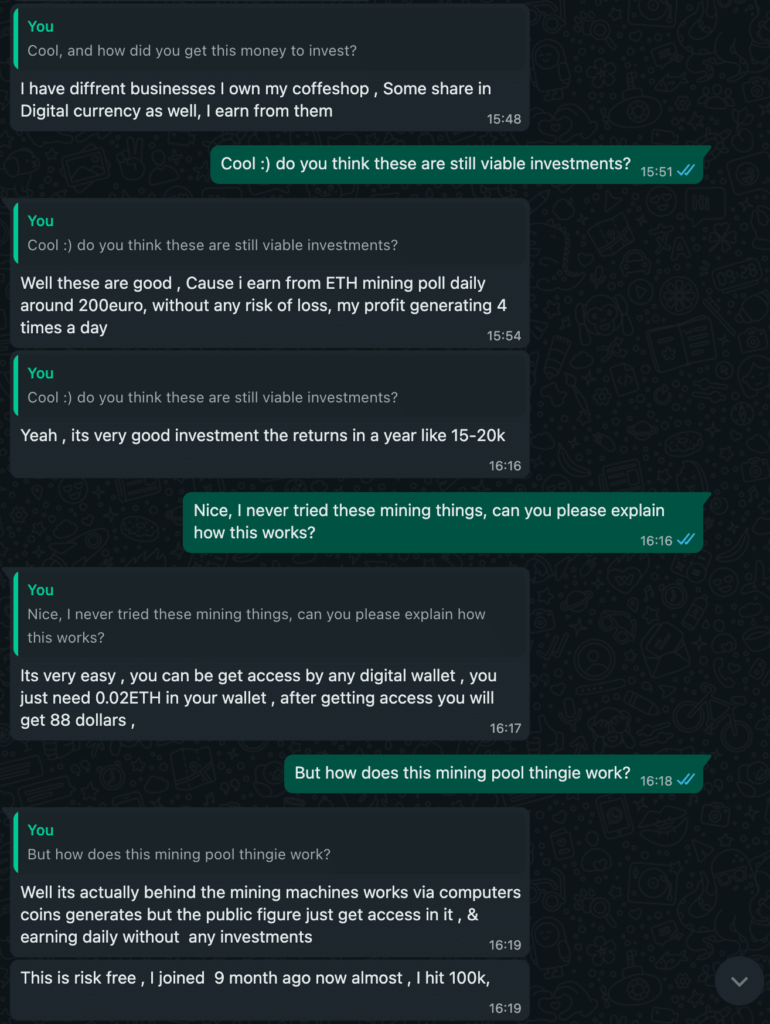
From then on, our chat got even more exciting… It turns out she was earning money from digital currency, around 200 EUR daily, and she was happy to share the details with me!
This had to be my lucky day 🙂
I could both meet this nice woman and earn some passive income on the side. RISK-FREE! This was too good to be true.
As an engineer, I am always interested in how things work, so I started asking her how this whole “digital currency” thing works, and if you copied your digital wallet file, could you spend the money twice? After all, the money’s in the wallet, which is a file, which you can copy…
In any case, I never got a proper answer on how the blockchain works. It seemed like this was not important for investing and earning money.


Time flew, I was trying to convince her to visit Budapest and meet me, while she sent more photos, but our chats always ended up at this “liquidity mining opportunity”. Personally, I was more interested in her coffee shop.
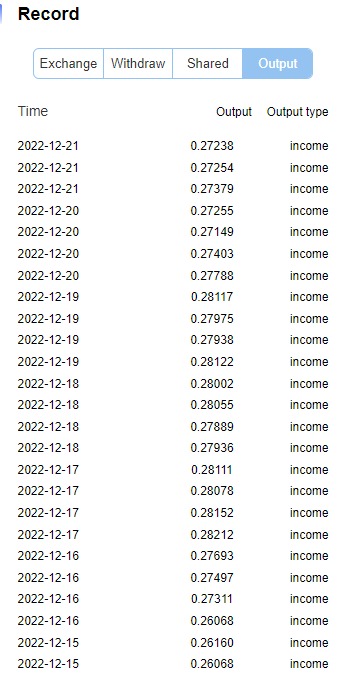
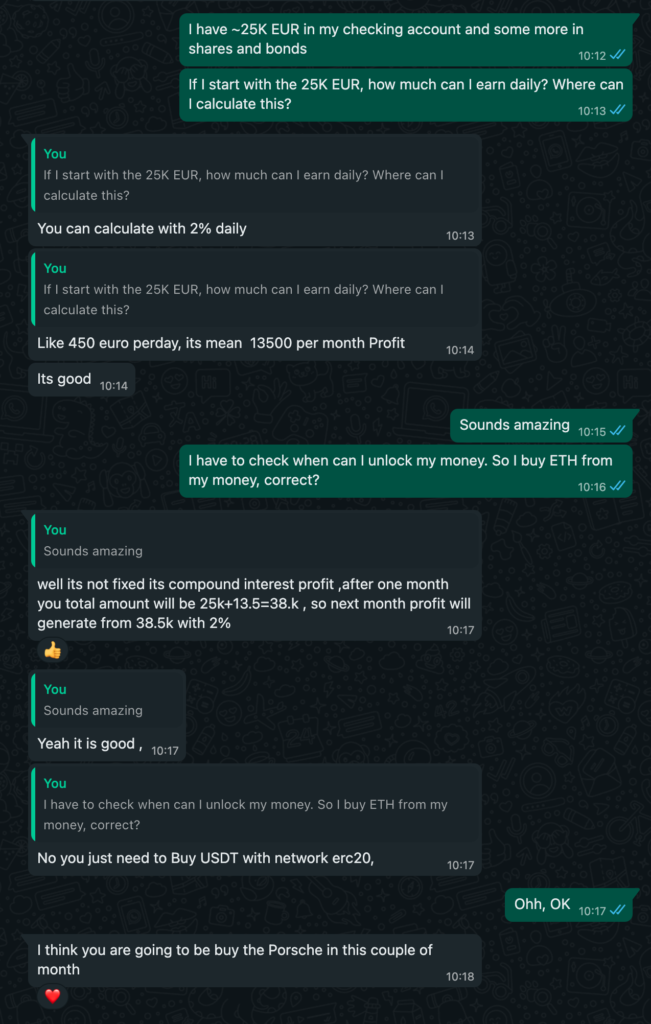
Since every chat ended up with “liquidity mining”, I gave up and told her I had a Metamask wallet and was interested in investing. This was the promise of how much I could earn.
I asked her if, based on what I had read on the Internet, I would also need to buy a fancy GPU to mine ETH. As it turns out, no, I didn’t – this was “liquidity mining.” And hey, I got new photos of her.

Oddly enough, whenever I mentioned Metamask, things did not go as planned. I was thinking about making the following conversation happen:
But I realized I was the problem.
I was too eager to jump into this “new crazy crypto income 100% risk-free”.
I did not listen to her when she told me to install a Trust or Safepal wallet, even when our romance was already going for three unforgettable weeks.
So I installed the Trust wallet app for iOS, and we were good to go. I got step-by-step instructions on how to buy Ethereum. She also warned me: “this is your personal information don’t show anyone.” How nice.
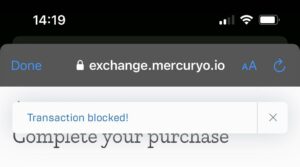
Sadly, my credit card issuer denied the transaction, and I couldn’t buy ETH. Five minutes later, a nice lady from my bank called to say that they had blocked my card and had the following questions:
- am I sure that I want to buy cryptocurrency?
- did someone tell me to buy cryptocurrency via chat or phone?
- did I get any investment tips from a closed Facebook group?
I told her everything was alright. I knew she would not understand my love romance with this random girl from WhatsApp. But even then, I could not buy ETH through this bank and had to use another credit card.
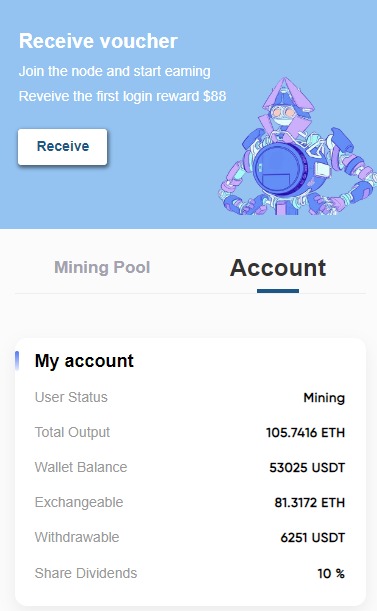
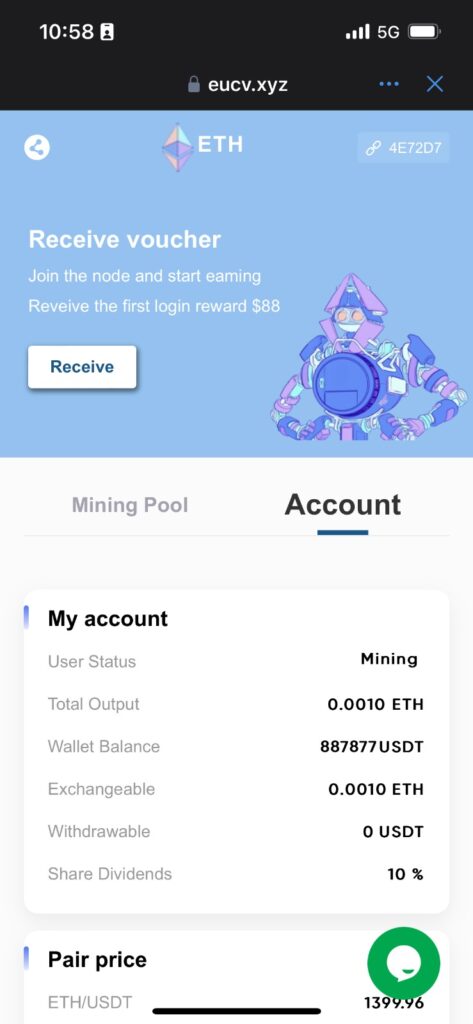
I spent $50 and then had to open a link in the Trust wallet’s built-in browser and click the Receive button to “Reveive the first login reward $88.”
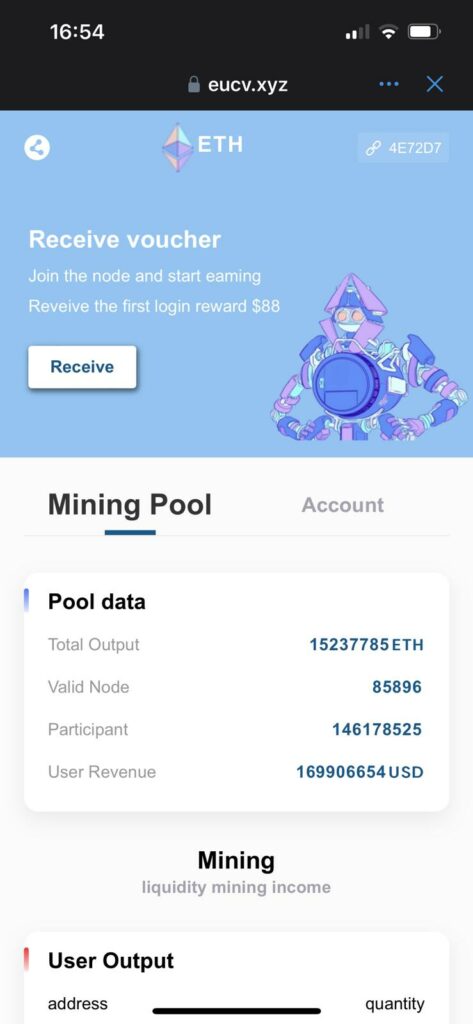

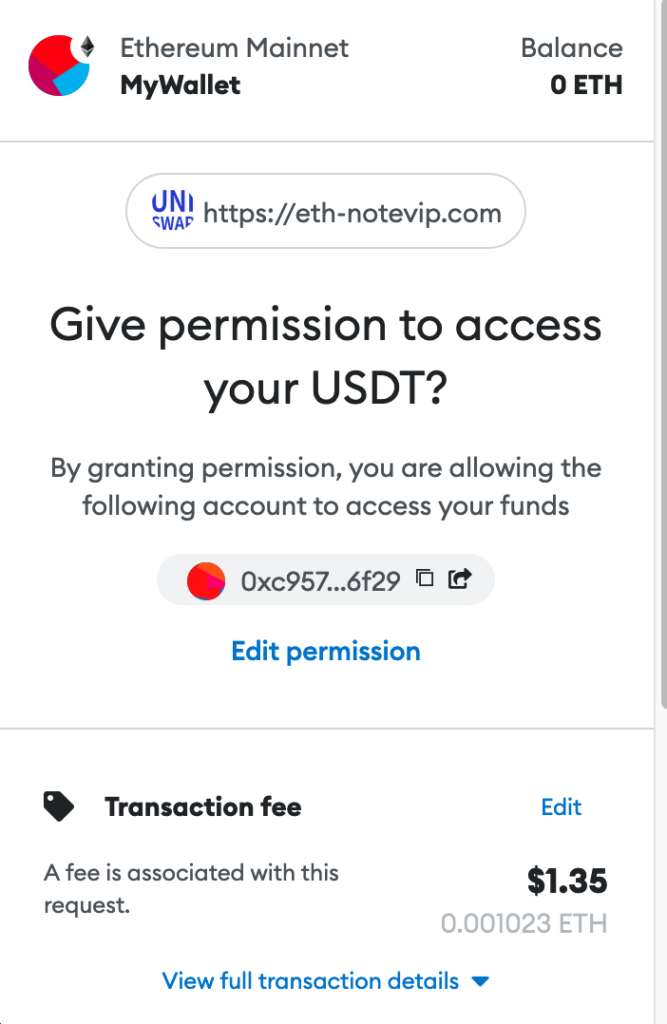
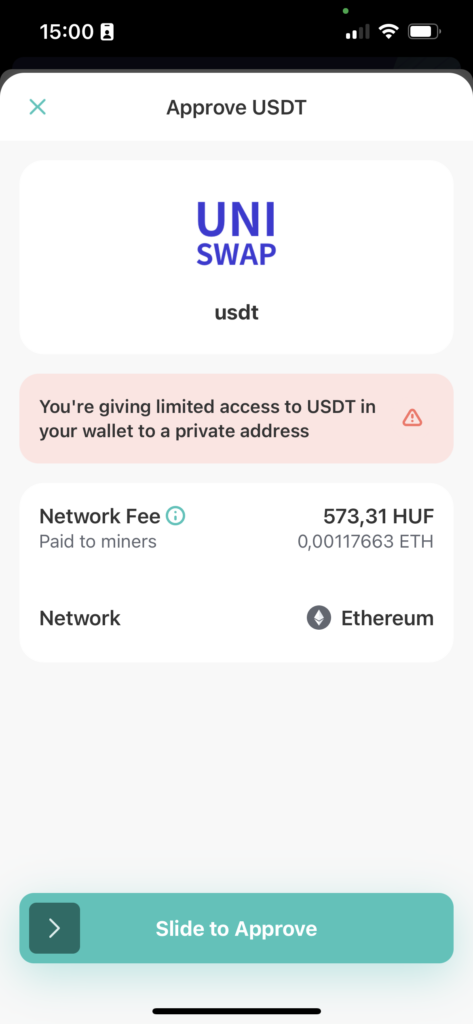
I had to spend a total of 1.67 USD in Ethereum transaction fees and, honestly, I had no idea what would happen next. With years of experience in cryptocurrency/Web3 related scams, I still had no idea what would happened if I clicked “Confirm” here. I tried opening the webpage in a desktop browser to debug this, but the app worked only in built-in wallet browsers.
I moved ~$30 out of this wallet to a safe one, since I was told that I only had to invest ~$20, but had ETH for $50 (a minimum amount I could buy through these crypto exchange providers), and clicked “Confirm”. Once the transaction was done and I had an etherscan.io address, I could finally see what was going on.

I had called a function on the USDT smart contract and approved an unknown smart contract to access ALL of the USDT in my wallet. USDT is a “stablecoin” where a company (Tether) promises that this crypto asset would have a 1:1 exchange ratio to USD.
But where were the $88 I was promised? After clicking on Exchange and Withdraw, my 88 USDT were in a “moderated” state.
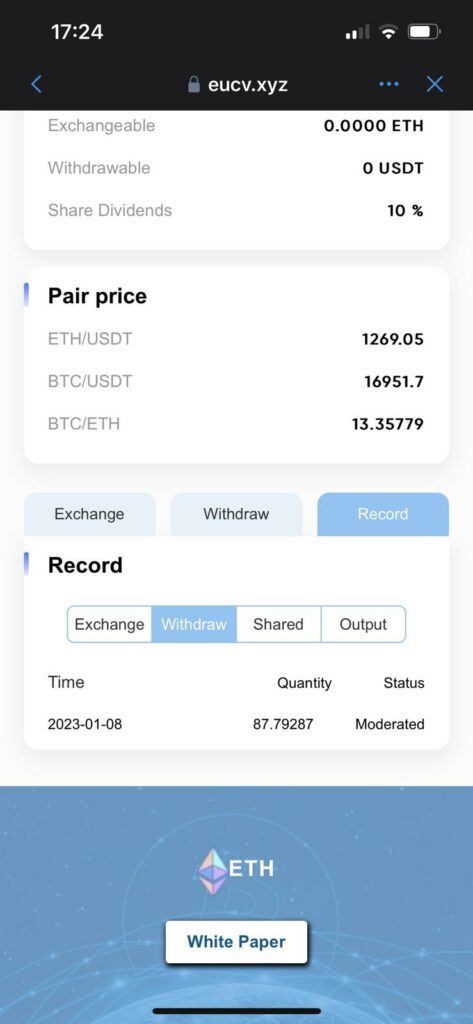
Meanwhile, the love of my life had an urgent meeting she had to attend. In the morning, I checked the Trust wallet and saw that I really got the 88 USDT. I believe someone manually approved the transaction in the backend.
And now, it was time to secure my gains and only continue the conversation for the LULZ.

First, I had to revoke their privileges. I opened the built-in browser in the Trust wallet, went to https://revoke.cash, and revoked the permission. Beware, there are revoke.cash copycat sites which try to scam you!
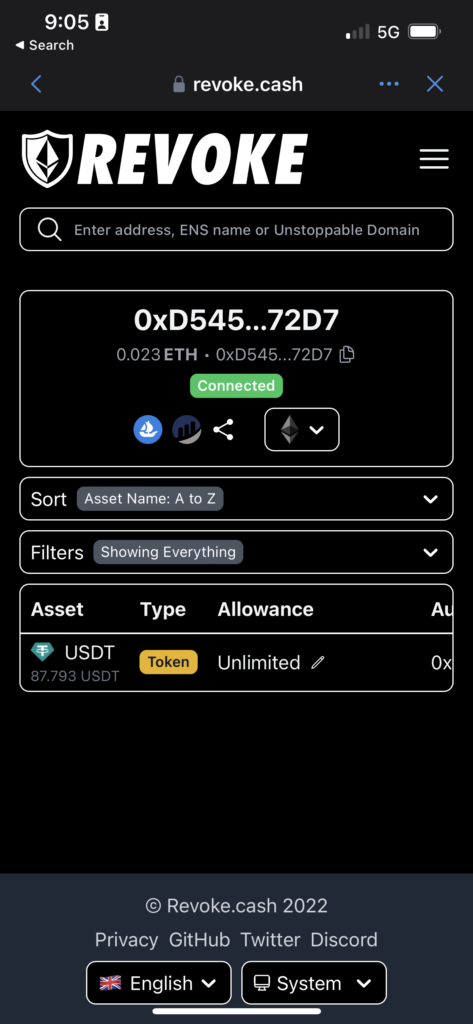
This was an important step from my side because without this they had “backdoor access” to all of the USDT stored in my wallet.
This scam is pretty smart and advanced because they never asked for my personal data, wallet private key/seed phrase, or credit card info. Even if it took three weeks to get there because of me…


Since she was under the weather, I tried to start a video call to cheer her up with my charming personality but, unfortunately, could connect with her.
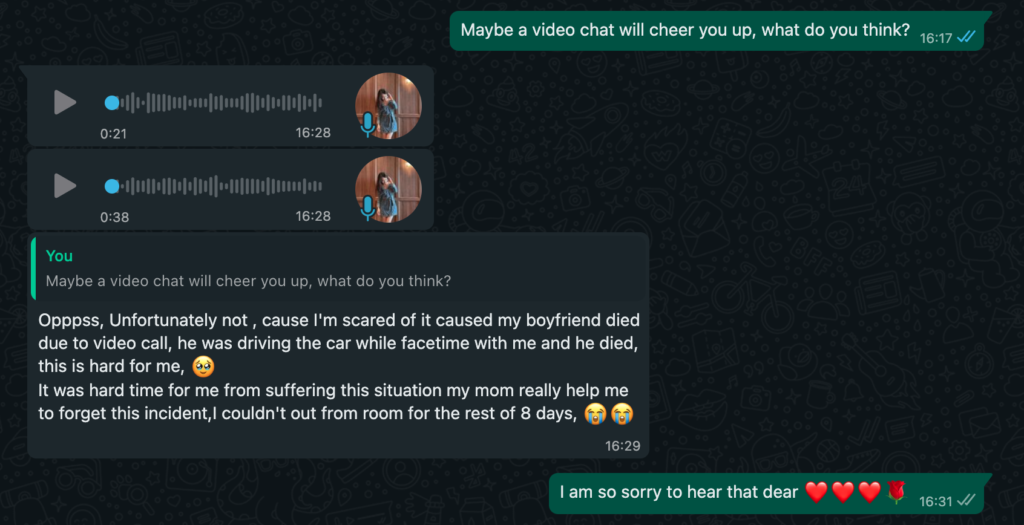
But I did get some voice recordings. Here is a sample.
Let us know on Linkedin/Mastodon/Twitter what accent this is.
This went on for a while. I was flexing my leet Photoshop skills and sent her the following fake screenshot, telling her I had added a ton of money to the wallet.

And got the following voice recordings back:
At this stage, I wasn’t acting like a regular victim, so I wondered what would have happened if I had “added” less money. Would the scammers allow me to withdraw some more? I don’t know. It seemed risky, and stealing from scammers is still stealing since I cannot give the money back to the people it was stolen from.


While I was waiting for the daily 2% profit, I wanted to know what she thought about scammers. Seems like we were on the same page 🙂
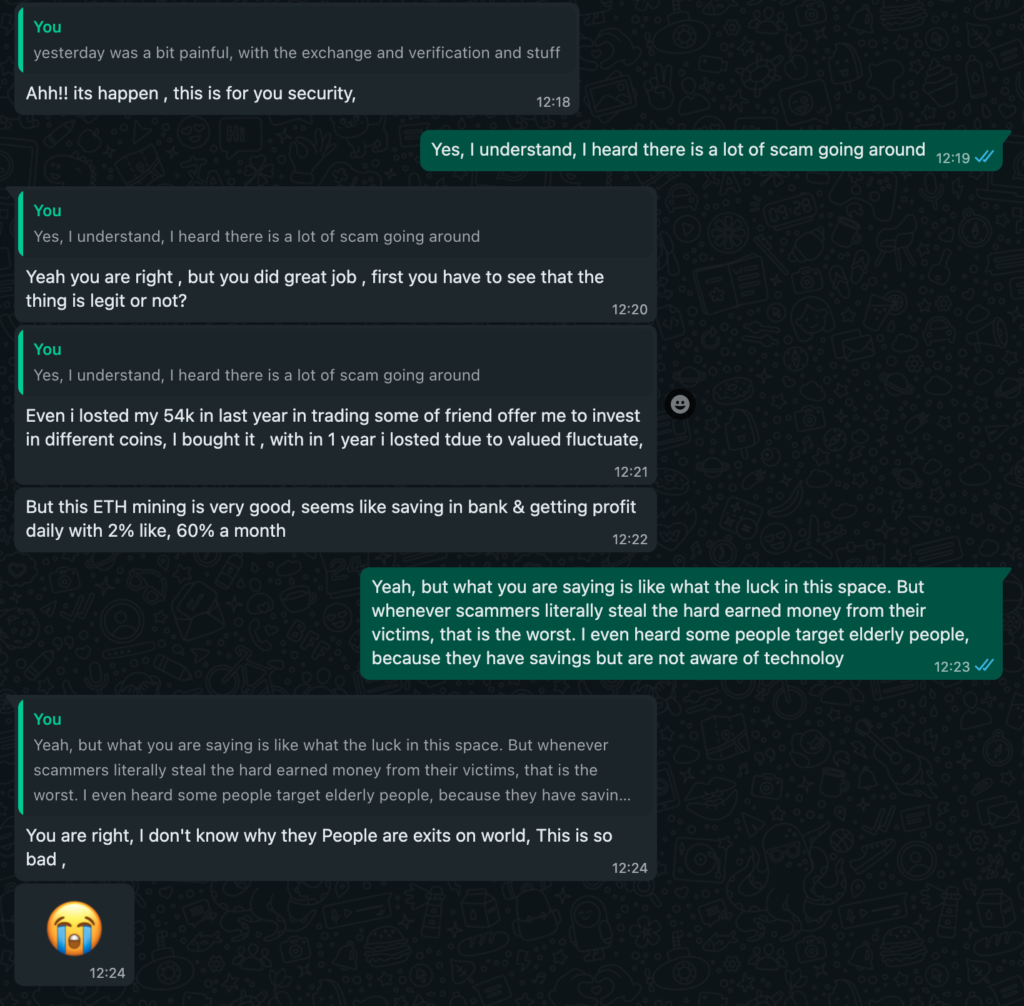
This chat went on for a while, and I finally figured out how to load the website on a desktop in Chrome, so I was able to modify the DOM and did not have to use Photoshop anymore.
My initial goal was to annoy them to a point where they realized I was playing with them, but this did not happen. So I finally gave up and told her I knew they were running a scam. Afterwards, we still had a nice chat, and I asked some questions, which she answered. These answers could be a lie or not. I am not sure, but I believe it’s mostly the truth.
She tells me she is from Cambodia, working on these scams from an office for three months already. She makes 1,200 USD per month which is a lot more than the average people earn there. She is not forced to scam people, but her family is pretty poor. And, last but not least, I sent her a grabify.link to get more info. Turns out she is probably using an Alibaba-based VPN, Asia/Bangkok GMT+7 timezone, Windows10 + Chrome. After this, I reported both numbers to WhatsApp. Hopefully, they will block them.
Conclusion
As mentioned in the beginning, do not try to repeat this process with a scammer. It can go bad easily. These scams are very sophisticated, the scammers are very persistent, and they can grab a lot of money. What is even worse, some people try to scam the victims after they have been scammed. They do this by running fake “recovery services”, promising people to get the funds back. Unfortunately, once scammed, there is no way to recover the assets.
Keeping the 88 USD felt wrong, so we transferred the same amount to https://kiva.org, so they could use this money for their operational expenses.
If you find this story useful, please share it with your friends/relatives/loved ones so that they don’t fall for a similar scam.
Technical details
Now that the fun story has ended, let’s look at the technical details. This type of scam is not new. A whole subreddit (not a thread!) discusses these types of ETH liquidity scams. The technical term for this type of scam is “pig butchering”. I don’t like calling people pigs, but that’s how it’s called.
Sometimes, I wonder who comes up with these technical terms…
What most people do not realize is that the victims lose a significant amount of money – based on the statistics from Global Anti Scam, the average loss per victim in the US was $210K.
I believe the biggest “vulnerability” was the Trust wallet app and its poor user interface. This issue is called blind signing, where the user does not know what they are about to confirm. Luckily, Metamask, Zengo, and other wallet software handle this better.
We checked to see similar scam websites and found a bunch of those. Some of these sites allowed us to interact with Metamask and Zengo, and this is what we saw.
- We reported the scammer’s phone numbers to WhatsApp as malicious.
- Reported the websites as a scam in Metamask, Trust, and Google Safebrowsing.
- Unfortunately, we can’t report the smart contract as malicious because the victim interacts with the trusted USDT smart contract.
- We could not report the scammer wallet as malicious on Etherscan, as there were issues with their form.
This wallet started its malicious activity in October 2022. And has already gained a significant amount of money. According to the blockchain, ~40K USD was already stolen and cashed out.
We don’t know where the photos used by the scammer are from, but we have already found some of them in another scam. It may be part of a package from a marketplace where people sell and buy photo albums of legitimate people and use them for fake profiles and scams. We believe this operation is not a one-man show. The first Whatsapp number is most likely used to lure victims in. The second number was used for the real scam. It makes sense to separate them because losing the number for the second account can be painful. We believe a boss is manually approving the outgoing 88 USDT or similar transactions. There are likely some developers/IT people that develop the website and take care of the infrastructure. Some JavaScript comments indicate that the original version of the scam website is from China.
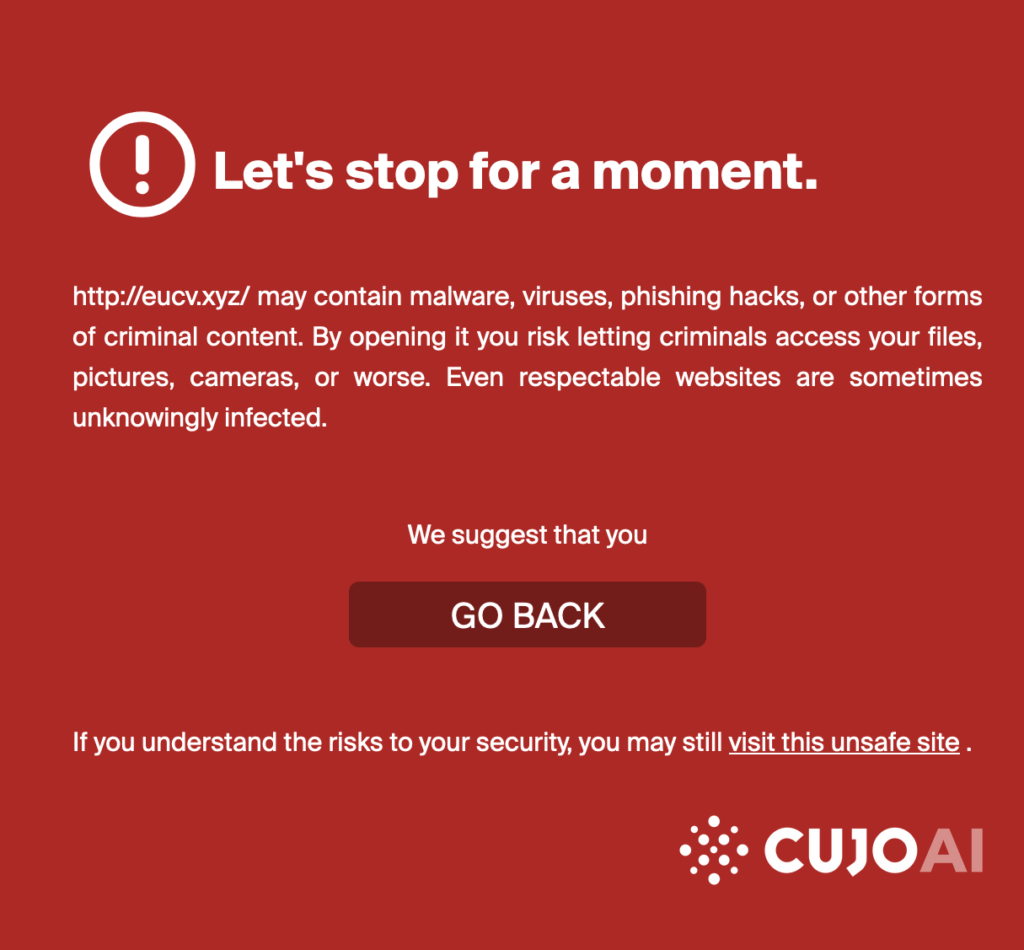
And this is how the website looks like on CUJO AI protected home networks, no matter if you are browsing from your desktop, mobile, Raspberry Pi, or Commodore 64.