Works Across Home
Wi-Fi and Mobile
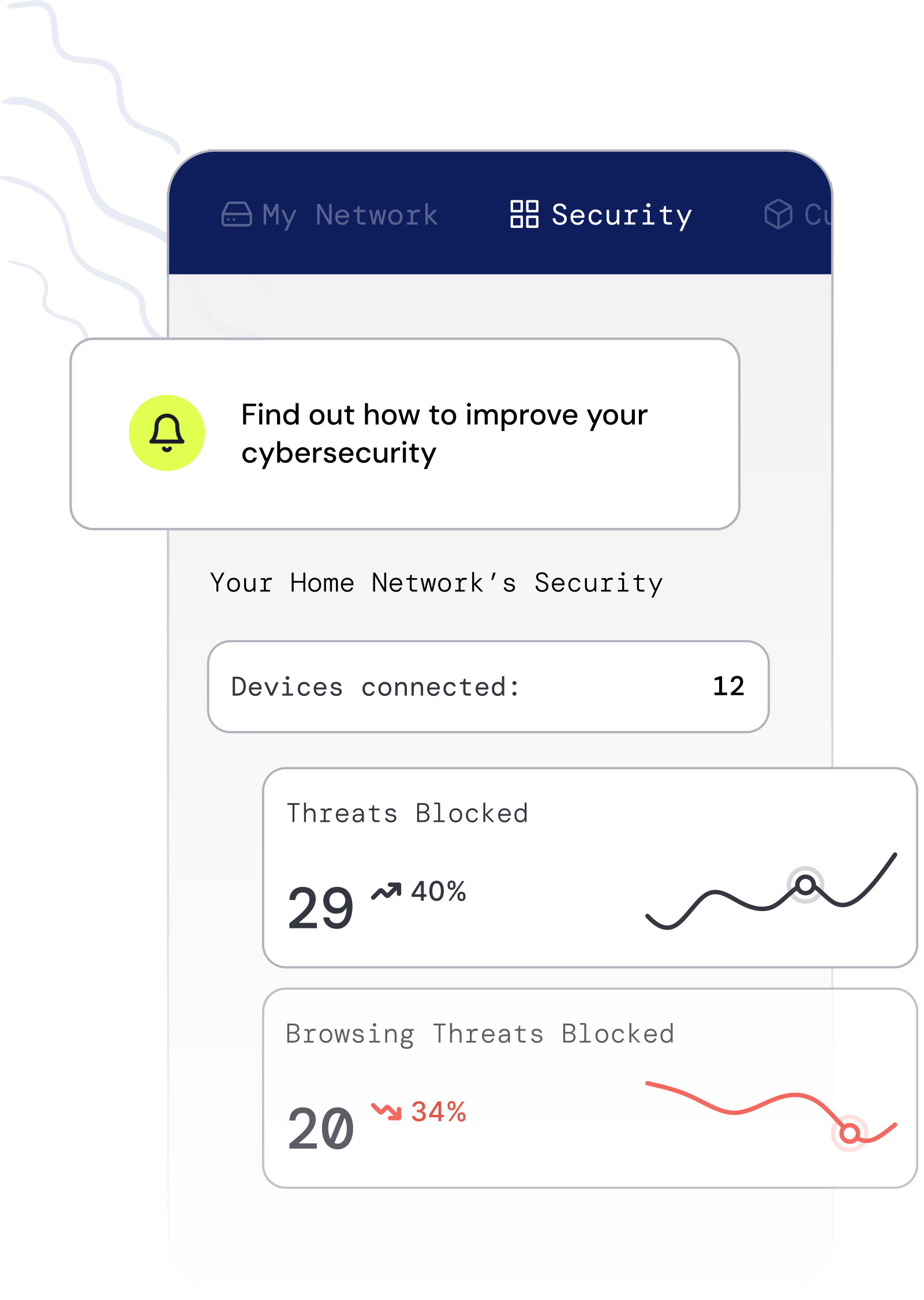
Protect your customers from threats both in and outside the home network with the combination of our router agent and mobile app SDK. Increase the value and positive engagement of your existing mobile app with fully integrated cyber security.