Residental Proxies ❤️ Amazon Fire TV Sticks
Introduction
Residential proxies are increasingly becoming a problem on the Internet. Remember the Taylor Swift concert where you had to buy a ticket second-hand at a higher price? Blame residential proxies. Are you annoyed with the ever-growing, complex CAPTCHA? Blame residential proxies. When your cutthroat TikTok competitor suddenly gets thousands of likes for no reason? Blame residential proxies.
Residential proxies are designed to make internet requests appear to originate from ordinary home networks. They do this by routing traffic through devices on those networks. Some companies advertise their residential proxy services as “legitimate”, but who knows what their clients use these accesses for. Others don’t even bother. For example, nowadays, more and more AI companies utilize residential proxies to bypass website operators’ anti-scraping protections.
Willing and unwilling participants
Some people willingly turn their home internet connection into a residential proxy for a monthly payment. But what they might not know is that they’re breaching the terms and conditions of their ISP’s Acceptable Usage Policy. Furthermore, some households unknowingly install and run residential proxies. The number one reason for this, according to multiple studies (Brian Krebs blog, Vo1d, Badbox) is Android-based smart TV boxes, such as the Superbox. And there are good reasons for that.
For residential proxy operators, the ideal device at home is easy to develop, inexpensive to buy, always on and always connected to the network, and hard to monitor. Nowadays, people turn to piracy to watch their favorite sports channels, TV shows, or anime. Long gone are the days when folks downloaded movies and TV shows via torrent. Piracy today is as simple as turning on the Android box, launching an app, and hitting play. But who is paying for these free services? There are bills to pay for these streaming servers, and the people using residential proxies are paying them. Kind of. If you’re OK with a complete stranger sitting in your living room and using your Wi-Fi to browse the Internet, we’re not going to judge you.
The Amazon Fire TV stick connection
In this article, we’d like to detail how Amazon Fire TV Sticks are connected to this topic. According to our data, Amazon Fire TV Sticks are the second-largest group of devices exhibiting residential proxy functionality. Why? Because Amazon is a trusted brand (for most people) that offers better-than-average-quality products via sideloading. In case you were wondering, the Superbox is the largest group. But that’s a story for another article.
Stores that deliver the types of apps you’d need to pirate online content are numerous. Recently, Amazon began cracking down on both malicious and piracy-related apps. Unfortunately, when we looked into this, we found that the current crackdown is not very effective because it relies on Android app package names. However, for app developers, it is trivial to change the package name and redistribute the same app (via Unlinked or similar) to users. An analogy would be an antivirus system detecting virus.exe but not totally_not_a_virus.exe, with the same file contents. When we first started installing piracy apps on the Fire TV Stick, it was rather hard to find any apps that triggered a warning.
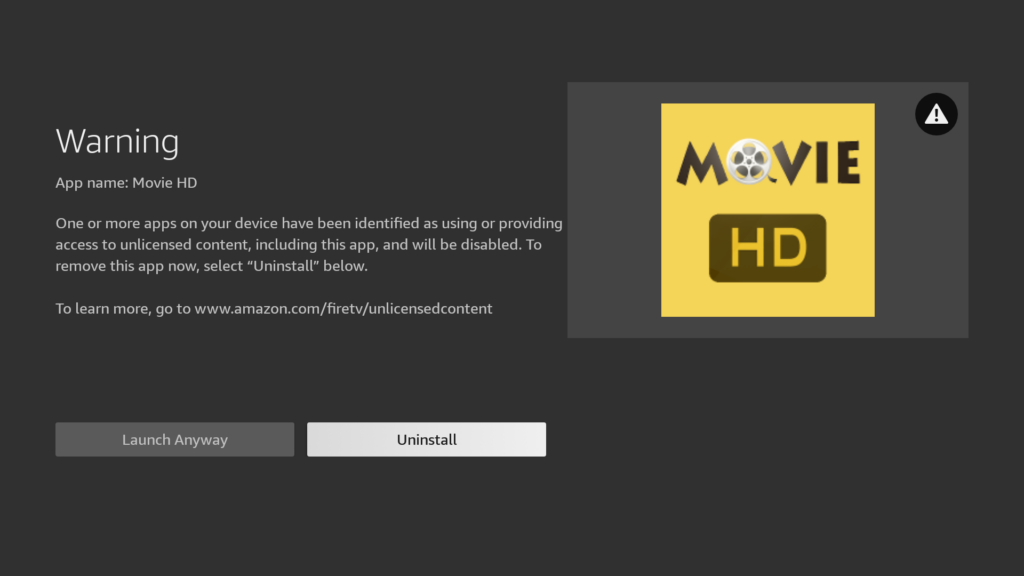
And in the beginning, for about a week, we were still able to launch the app. After a while, the app was blocked.

We were able to determine, via network traffic analysis, that our Amazon Fire TV Stick had indeed become a residential proxy. It made connections to eBay, TicketMaster, Outlook and other sites.
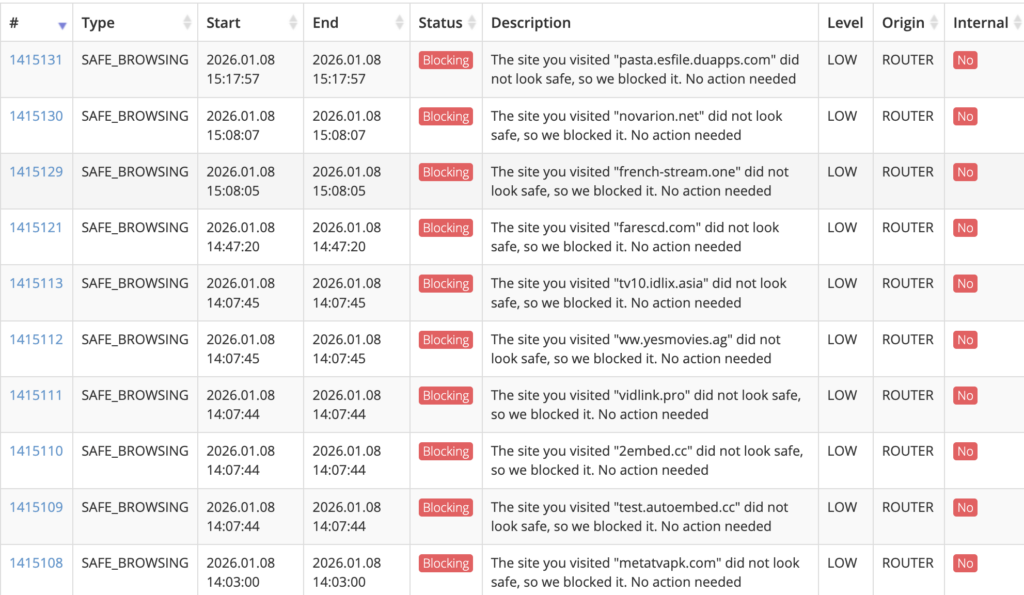
The following network traffic was immediately flagged as suspicious/malicious by our product. This traffic started to flow after installing just a few of these piracy apps.
Evading detection
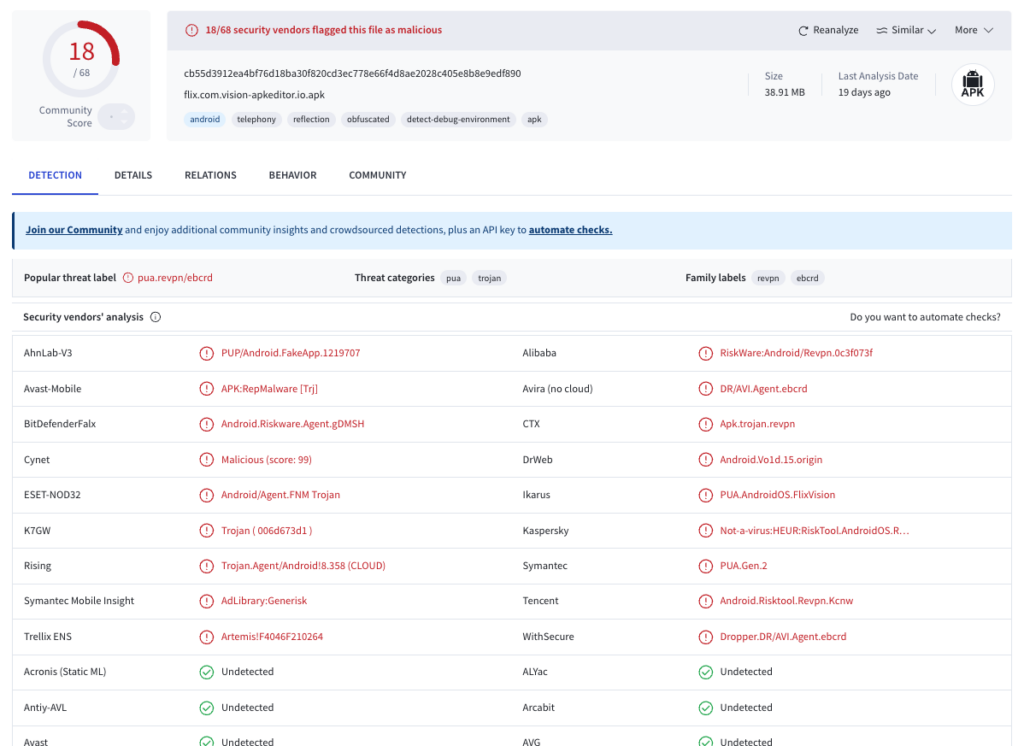
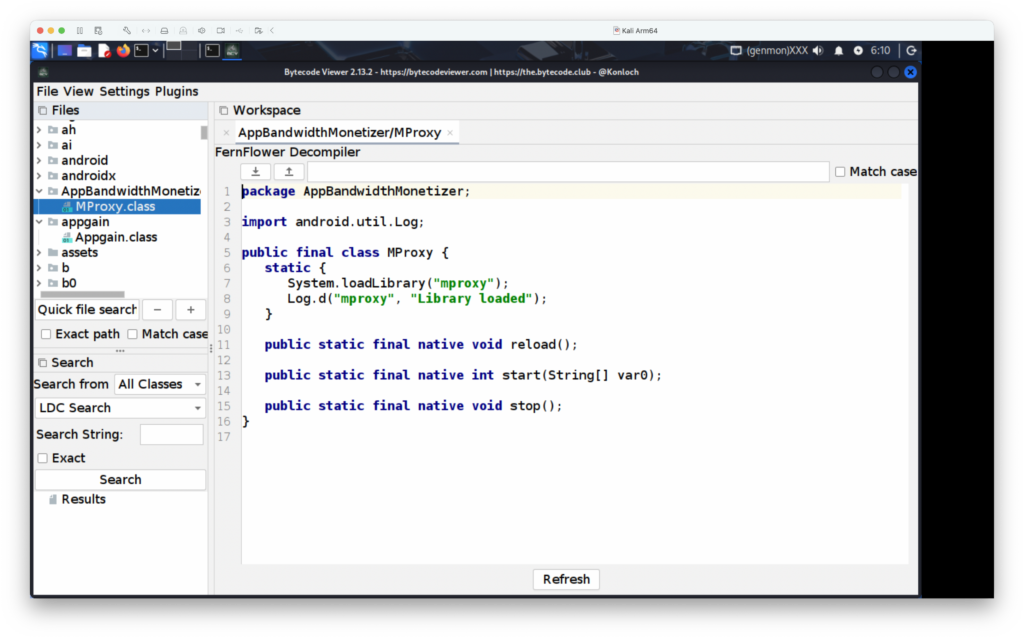
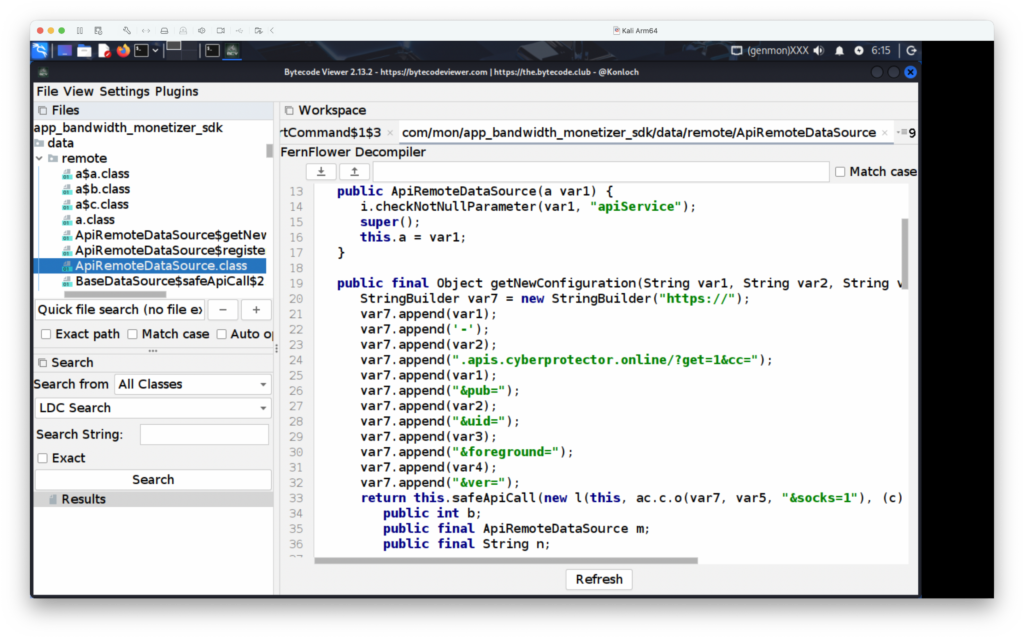
Our colleague, Andras, checked the APK binaries and quickly found the following non-obfuscated code in them. Not all of the examined apps were marked as detected on VirusTotal. https://www.virustotal.com/gui/file/cb55d3912ea4bf76d18ba30f820cd3ec778e66f4d8ae2028c405e8b8e9edf890
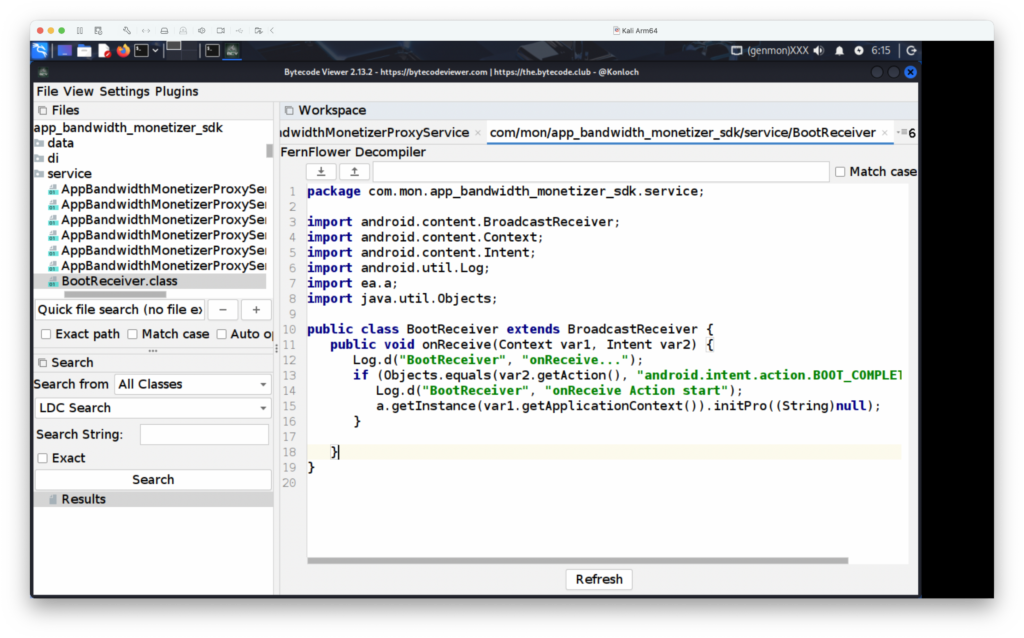
When we started reverse engineering the files, I was not expecting to see strings like “AppBandwidthMonetizer/MProxy“. Another interesting feature of many of the apps we examined was that they registered for the BootReceiver intent, meaning the code runs only when the device starts and performs untrustworthy operations only after a reboot. This has two benefits for residential proxy operators: first, they don’t have to wait for the user to start the app, and second, APK malware analysis sandboxes usually don’t restart the environment, so it is a free bypass for the operators.
What comes next?
Even though the current crackdown on piracy apps from Amazon is not very effective, it still annoys people, and we believe most will move to shady platforms like Superbox and other cheap Android boxes from unknown vendors. And with these Android smart TV boxes, you never know what’s already inside the operating system, or what comes with the next update. But one thing is true: if you are not paying for the streaming content with money, chances are you are paying in ways you don’t realize. You are paying for it, but in a different way. Be wary!
Bonus!
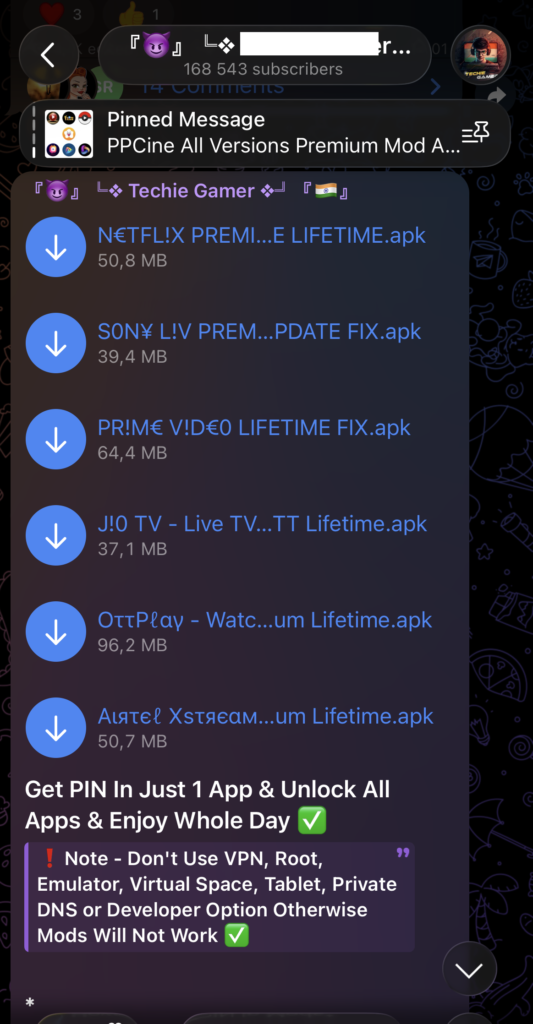
By checking the certificate used to sign one of the APKs, we found a Telegram channel that did not disappoint.